30 darmowych spinów bez depozytu w Energy Casino
April 5, 2025Logowanie w Vulkan Casino: Zaloguj Się w Kasyno Online
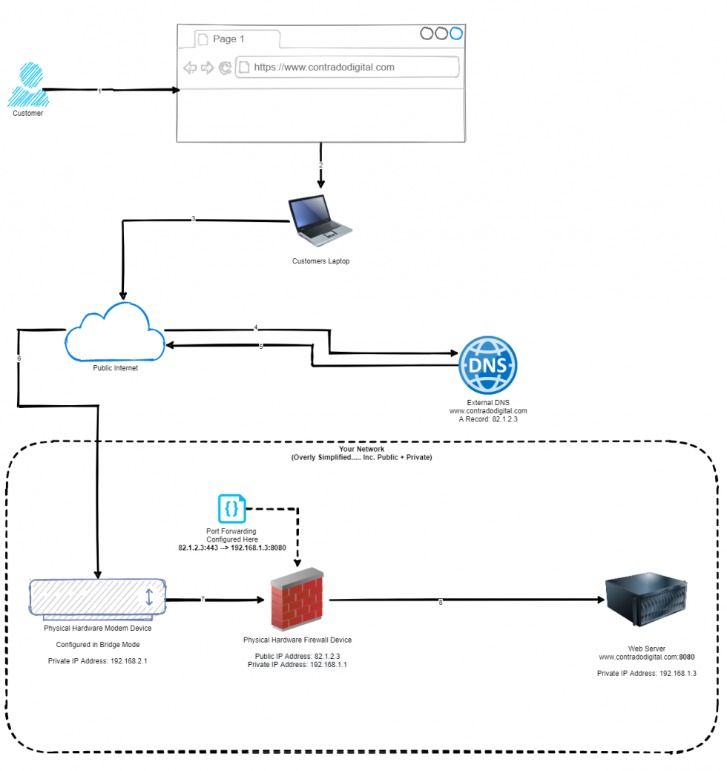
April 8, 2025It visually represents how different parts are related, helping you design and implement effective firewall rules. You must define firewall rules that specify what traffic must be allowed or blocked. Only community packets that match the configured guidelines are allowed through. For instance, a rule could allow TCP traffic on port 80 while blocking other ports.
- The other arguments you should find your operating companies are -p, -l, -u, -n, and -t, which you may be able to provide as -plunt.
- To keep away from a conflict of firewall rules and their correct configuration, you should understand the working procedures of present firewalls.
- Monitor site visitors in real-time – Set up monitoring instruments to track real-time visitors through the firewall, enabling quick responses to any suspicious exercise.
- It acts as a vigilant sentinel, inspecting each incoming and outgoing packet of knowledge, allowing solely approved visitors to pass whereas blocking malicious or suspicious activity.
Step 1: Hook Up With Your Server
Studying the way to configure a firewall in your VPS is crucial to ensuring that your server only communicates with trusted IP addresses and applications. By blocking suspicious visitors and securing open ports, a firewall minimizes vulnerabilities and strengthens your server’s defenses against cyber threats. A firewall is a safety device that acts as a barrier between your internet server and the skin world.
Configuring Inbound And Outbound Rules
Careful configuration enhances safety whereas permitting desired connections. One frequent oversight in firewall configuration just isn’t altering the default settings. Firewalls usually 日本vps include publicly known producer defaults, making them vulnerable. Ensure all defaults, together with passwords, usernames, and IP addresses, are custom to prevent unauthorized entry.
Configure your firewall to limit entry to the DMZ and carefully control site visitors between the DMZ and the interior community. IPS actively displays network visitors for indicators of malicious activity and takes quick action to dam or mitigate assaults. This can include dropping packets, resetting connections, or alerting directors. Firewall logging and monitoring are essential for sustaining security over time. They provide insight into traffic patterns, rule effectiveness, and potential safety events. Firewall guidelines define which traffic can move between network zones, based mostly on standards similar to IP handle, protocol, port quantity, and direction of data move (inbound or outbound).
